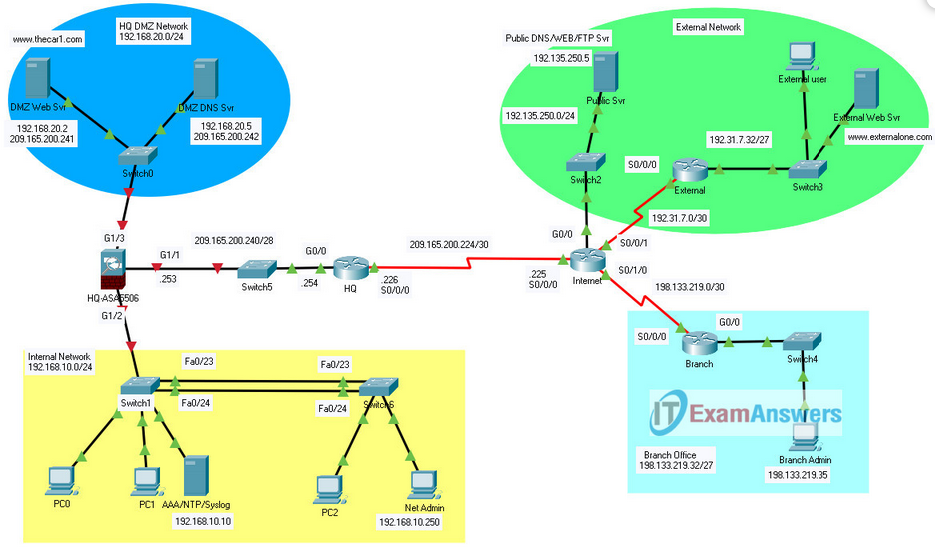
Network Security – Practice PT Skills Assessment (PTSA) Answers
Objectives In this practice Packet Tracer Skills Based Assessment, you will: Configure an ASA firewall to implement security policies. Configure Layer 2 security on a LAN switch. Configure a site-to-site IPsec VPN
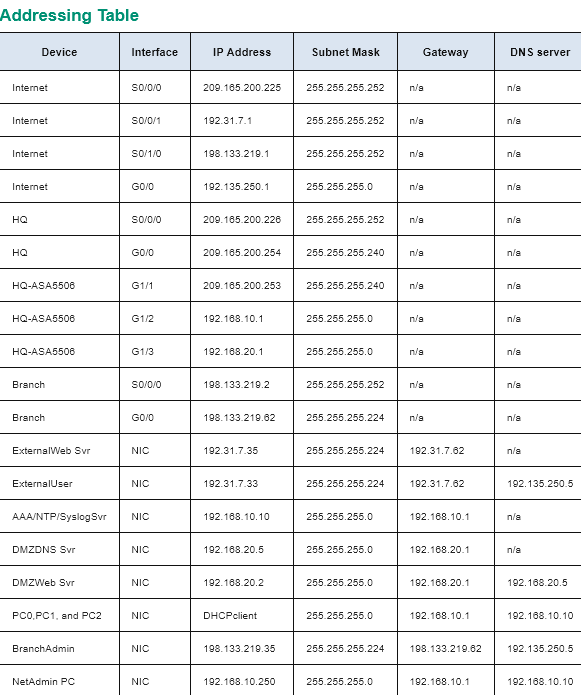
Part 1: Configure the ASA 5506-X
Step 1: Configure Basic Settings on the ASA device.
Device: HQ-ASA5506
enable
Thecar1Admin
conf term
domain-name thecar1.com
hostname HQ-ASA5506
interface g1/1
nameif OUTSIDE
security-level 1
ip address 209.165.200.253 255.255.255.240
no shutdown
interface g1/2
nameif INSIDE
security-level 100
ip address 192.168.10.1 255.255.255.0
no shutdown
interface g1/3
nameif DMZ
security-level 70
ip address 192.168.20.1 255.255.255.0
no shutdown
exit
Step 2: Configure the DHCP service on the ASA device for the internal network.
Device: HQ-ASA5506
dhcpd address 192.168.10.25-192.168.10.35 INSIDE
dhcpd dns 192.168.10.10 interface INSIDE
dhcpd option 3 ip 192.168.10.1
dhcpd enable INSIDE
Step 3: Configure routing on the ASA.
Device: HQ-ASA5506
route OUTSIDE 0.0.0.0 0.0.0.0 209.165.200.254
Step 4: Configure Secure Network Management for the ASA Device.
Device: HQ-ASA5506
ntp authenticate
ntp authentication-key 1 md5 corpkey
ntp server 192.168.10.10
ntp trusted-key 1
Device: HQ-ASA5506
username Car1Admin password adminpass01
aaa authentication ssh console LOCAL
crypto key generate rsa modulus 1024
yes
ssh 192.168.10.250 255.255.255.255 INSIDE
ssh timeout 20
Step 5: Configure NAT Service for the ASA device for both INSIDE and DMZ networks.
Device: HQ-ASA5506
object network INSIDE-nat
subnet 192.168.10.0 255.255.255.0
nat (inside,outside) dynamic interface
exit
configure terminal
object network DMZ-web-server
host 192.168.20.2
nat (dmz,outside) static 209.165.200.241
exit
configure terminal
object network DMZ-dns-server
host 192.168.20.5
nat (dmz,outside) static 209.165.200.242
exit
Step 6: Configure ACL on the ASA device to implement the Security Policy.
Device: HQ-ASA5506
configure terminal
access-list NAT-IP-ALL extended permit ip any any
access-group NAT-IP-ALL in interface OUTSIDE
access-group NAT-IP-ALL in interface DMZ
access-list OUTSIDE-TO-DMZ extended permit tcp any host 209.165.200.241 eq 80
access-list OUTSIDE-TO-DMZ extended permit tcp any host 209.165.200.242 eq 53
access-list OUTSIDE-TO-DMZ extended permit udp any host 209.165.200.242 eq 53
access-list OUTSIDE-TO-DMZ extended permit tcp host 198.133.219.35 host 209.165.200.241 eq ftp
end
copy running-config startup-config
Part 2: Configure Layer 2 Security on a Switch
Step 1: Disable Unused Switch Ports
Device: Switch 1
enable
conf t
interface range f0/2-4, f0/6-9, f0/11-22, g0/2
shutdown
switchport mode access
switchport nonegotiate
Step 2: Implement Port Security
Device: Switch 1
interface range f0/1, f0/5, f0/10
switchport mode access
switchport port-security
switchport port-security maximum 2
switchport port-security mac-address sticky
switchport port-security violation restrict
switchport nonegotiate
Step 3: Implement STP Security
Device: Switch 1
interface range f0/1, f0/5, f0/10, g0/1
spanning-tree bpduguard enable
spanning-tree portfast
end
copy running-config startup-config
Part 3: Configure a Site-to-Site IPsec VPN between the HQ and the Branch Routers
Device: HQ Router
Username: CORPADMIN
Password: NetSec-Admin1
enable
Password: RTR-AdminP@55
conf ter
access-list 120 permit ip 209.165.200.240 0.0.0.15 198.133.219.32 0.0.0.31
crypto isakmp policy 10
encryption aes 256
hash sha
authentication pre-share
group 2
lifetime 1800
exit
crypto isakmp key Vpnpass101 address 198.133.219.2
crypto ipsec transform-set VPN-SET esp-aes esp-sha-hmac
crypto map VPN-MAP 10 ipsec-isakmp
match address 120
set transform-set VPN-SET
set peer 198.133.219.2
set pfs group2
set security-association lifetime seconds 1800
exit
int s0/0/0
crypto map VPN-MAP
end
copy running-config startup-config
Device: Branch Router
Username: CORPADMIN
Password: NetSec-Admin1
enable
Password: RTR-AdminP@55
conf ter
access-list 120 permit ip 198.133.219.32 0.0.0.31 209.165.200.240 0.0.0.15
crypto isakmp policy 10
encryption aes 256
hash sha
authentication pre-share
group 2
lifetime 1800
exit
crypto isakmp key Vpnpass101 address 209.165.200.226
crypto ipsec transform-set VPN-SET esp-aes esp-sha-hmac
crypto map VPN-MAP 10 ipsec-isakmp
match address 120
set transform-set VPN-SET
set peer 209.165.200.226
set pfs group2
set security-association lifetime seconds 1800
exit
int s0/0/0
crypto map VPN-MAP
end
copy running-config startup-config
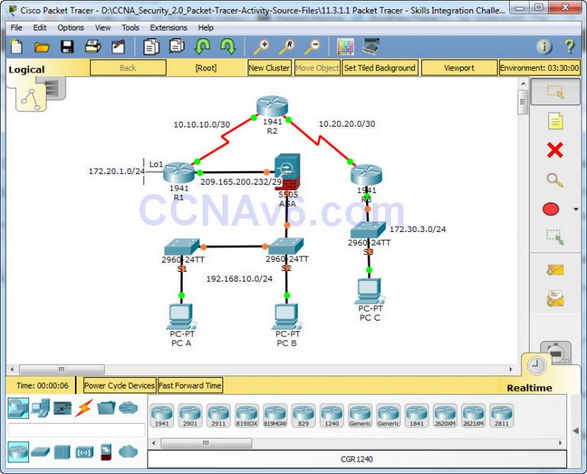
1.3.1.1-packet-tracer-skills-integration-challenge-answers
!-------------------------------
!Configure Basic Router Security
!-------------------------------
!R1
conf t
security passwords min-length 10
enable secret ciscoenapa55
service password-encryption
line console 0
password ciscoconpa55
exec-timeout 15 0
login
logging synchronous
banner motd $Unauthorized access strictly prohibited and prosecuted to the full
extent of the law!$
end
!R2
conf t
enable secret ciscoenapa55
line vty 0 4
password ciscovtypa55
exec-timeout 15 0
login
end
!-------------------------
!Configure Switch Security
!-------------------------
!S1
conf t
service password-encryption
enable secret ciscoenapa55
line console 0
password ciscoconpa55
exec-timeout 5 0
login
logging synchronous
line vty 0 15
password ciscovtypa55
exec-timeout 5 0
login
banner motd $Unauthorized access strictly prohibited and prosecuted to the full
extent of the law!$
end
!Trunking
!S1 and S2
conf t
interface FastEthernet 0/1
switchport mode trunk
switchport trunk native vlan 99
switchport nonegotiate
end
!S1 Port Security
conf t
interface FastEthernet 0/6
switchport mode access
spanning-tree portfast
spanning-tree bpduguard enable
shutdown
switchport port-security
switchport port-security mac-address sticky
no shutdown
interface range f0/2 – 5 , f0/7 – 24 , g0/1 - 2
shutdown
end
!----------------------------------
!Configure AAA Local Authentication
!----------------------------------
!R1
conf t
username Admin01 privilege 15 secret Admin01pa55
aaa new-model
aaa authentication login default local enable
end
!-------------------------
!Configure SSH
!-------------------------
!R1
conf t
ip domain-name ccnasecurity.com
crypto key generate rsa
1024
ip ssh version 2
line vty 0 4
transport input ssh
end
!----------------------------
!Secure Against Login Attacks
!----------------------------
!R1
conf t
login block-for 60 attempts 2 within 30
login on-failure log
!---------------------------------
!Configure Site-to-Site IPsec VPNs
!---------------------------------
!R1
conf t
access-list 101 permit ip 172.20.1.0 0.0.0.255 172.30.3.0 0.0.0.255
crypto isakmp policy 10
encryption aes 256
authentication pre-share
hash sha
group 5
lifetime 3600
exit
crypto isakmp key ciscovpnpa55 address 10.20.20.1
crypto ipsec transform-set VPN-SET esp-aes 256 esp-sha-hmac
crypto map CMAP 10 ipsec-isakmp
set peer 10.20.20.1
set pfs group5
set transform-set VPN-SET
match address 101
exit
interface S0/0/0
crypto map CMAP
end
!R3
conf t
access-list 101 permit ip 172.30.3.0 0.0.0.255 172.20.1.0 0.0.0.255
crypto isakmp policy 10
encryption aes 256
authentication pre-share
hash sha
group 5
lifetime 3600
exit
crypto isakmp key ciscovpnpa55 address 10.10.10.1
crypto ipsec transform-set VPN-SET esp-aes 256 esp-sha-hmac
crypto map CMAP 10 ipsec-isakmp
set peer 10.10.10.1
set transform-set VPN-SET
match address 101
exit
interface S0/0/1
crypto map CMAP
end
!-----------------------------------
!Configure Firewall and IPS Settings
!-----------------------------------
!R3
conf t
!Firewall configs
zone security IN-ZONE
zone security OUT-ZONE
access-list 110 permit ip 172.30.3.0 0.0.0.255 any
access-list 110 deny ip any any
class-map type inspect match-all INTERNAL-CLASS-MAP
match access-group 110
exit
policy-map type inspect IN-2-OUT-PMAP
class type inspect INTERNAL-CLASS-MAP
inspect
zone-pair security IN-2-OUT-ZPAIR source IN-ZONE destination OUT-ZONE
service-policy type inspect IN-2-OUT-PMAP
exit
interface g0/1
zone-member security IN-ZONE
exit
interface s0/0/1
zone-member security OUT-ZONE
end
!IPS configs
mkdir ipsdir
conf t
ip ips config location flash:ipsdir
ip ips name IPS-RULE
ip ips signature-category
category all
retired true
exit
category ios_ips basic
retired false
exit
interface s0/0/1
ip ips IPS-RULE in
!--------------------------------------------------
!Configure ASA Basic Security and Firewall Settings
!--------------------------------------------------
!CCNAS-ASA
enable
conf t
interface vlan 1
nameif inside
security-level 100
ip address 192.168.10.1 255.255.255.0
interface vlan 2
nameif outside
security-level 0
no ip address dhcp
ip address 209.165.200.234 255.255.255.248
exit
hostname CCNAS-ASA
domain-name ccnasecurity.com
enable password ciscoenapa55
username admin password adminpa55
aaa authentication ssh console LOCAL
ssh 192.168.10.0 255.255.255.0 inside
ssh 172.30.3.3 255.255.255.255 outside
ssh timeout 10
dhcpd address 192.168.10.5-192.168.10.30 inside
dhcpd enable inside
route outside 0.0.0.0 0.0.0.0 209.165.200.233
object network inside-net
subnet 192.168.10.0 255.255.255.0
nat (inside,outside) dynamic interface
exit
conf t
class-map inspection_default
match default-inspection-traffic
exit
policy-map global_policy
class inspection_default
inspect icmp
exit
service-policy global_policy global
IF it isnt 100% because R3 110 ACL
R3(config)#no access-list 110
R3(config)#access-list 110 permit ip 172.30.3.0 0.0.0.255 any